How Veeam Strengthens Cyber Resilience Through Intelligent Recovery Systems
Modern organizations depend on secure data flow to keep operations steady and reliable. Veeam supports this need by offering reliable backup and quick restore options that protect valuable information. Strong planning with smart tools helps reduce risks and improve response time when issues arise, ensuring systems remain stable and protected with Veeam.
Fast Data Restoration Methods
Quick recovery plays a key role in reducing downtime and keeping operations active. Systems are designed to restore files instantly without long waiting periods.
- Rapid file recovery ensures minimal downtime during unexpected data loss
- Instant restore options reduce delay and support continuous workflow stability
- Secure backup copies allow safe retrieval without affecting original data
- Automated recovery testing improves readiness during critical failure situations
- Reliable restore processes maintain system balance and operational continuity
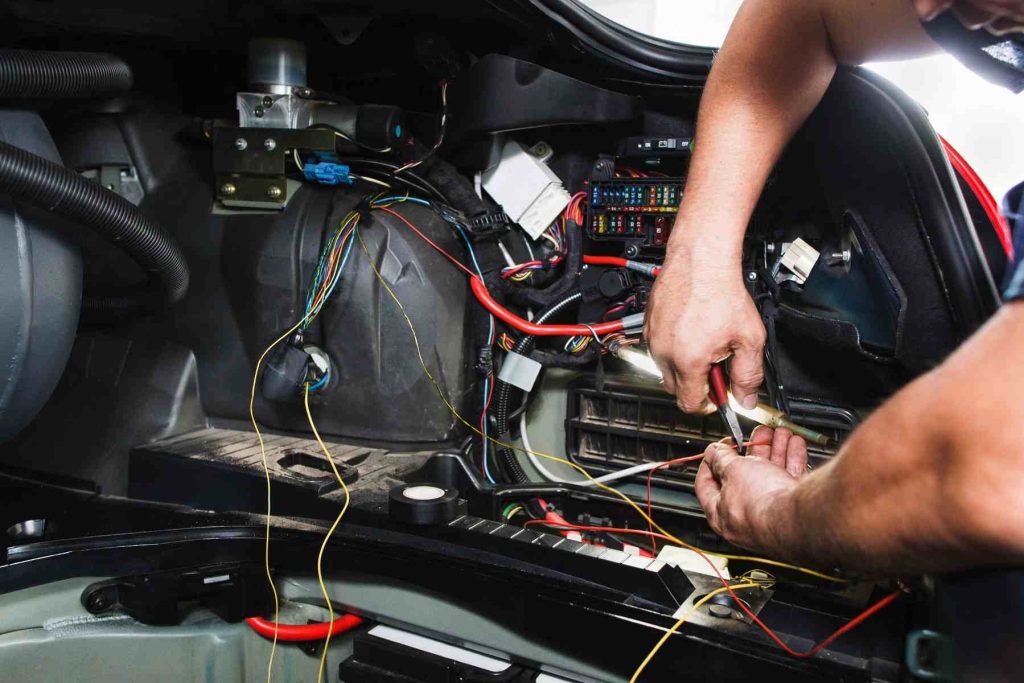
Automated Threat Detection Systems
Security improves when systems can detect unusual activity early and respond quickly. Built-in monitoring tracks patterns and alerts users about possible threats. Veeam enhances protection by combining smart detection with fast response actions. This reduces damage and ensures that systems stay protected without constant manual checks.

Scalable Data Protection Design
Flexible design allows systems to grow without losing efficiency or control. It adapts to changing needs while maintaining consistent backup and recovery performance. Storage can expand smoothly without affecting existing processes.
Reliable protection depends on combining smart backup methods with quick restore capabilities. Strong monitoring helps identify risks early while flexible design supports future growth without stress. Clear planning ensures faster action during disruptions and keeps operations running smoothly.
FAQ
What makes recovery systems more reliable during unexpected system failures?
Smart automation and quick restore options ensure stable recovery during issues.
Why is early threat detection important for maintaining secure data systems?
Early alerts reduce damage and allow faster response to possible risks.
How does scalable design help manage growing data protection needs effectively?
Flexible systems adjust easily and maintain performance as data volume increases.